“Cyber war” is a term that is in recent days used so liberally that people may often wonder if these words are as menacing as they sound or used only as a tool to incite fear as a way to control a society that increasingly depends on technology.
How we prepare and respond to cyber attacks depends on whether we believe we are in cyber war. It influences how we estimate the risks, potential impacts, or insurance premiums. Preparation for and response to cyber war implies government involvement and that might mean handing over the control of our networks to government. If we feel that the government should be responsible for preparation, we might not implement all the controls we otherwise would. Cyber war is a term with serious implications behind it. So are we really in the midst of cyber war(s)?
This post was originally published on my old blog. The postings on this site are my own and don’t necessarily represent IBM’s positions, strategies or opinions.
It is no secret that people are interested in what impact a cyber war could have on the world they live in. Cyber war is the new security topic du jour. Over last few years the amount of books, articles, movies, web sites dedicated to cyber war are growing exponentially.
So why such a burst in interest?
It may have something to do with media proclaiming that we are in the midst of cyber war and government officials pegging the possibility of a cyber war as a current problem that is escalating and that would soon reach critical limits.
U.S Defense Secretary Leon Panetta spoke bluntly to the American people as he warned of the growing danger of cyber warfare and its potential to cripple critical infrastructure.
In an interview with Smithsonian Richard Clarke, America’s longtime counter-terrorism czar warns that the cyber wars have already begun—and that we might be losing.
General Keith Alexander, head of the Pentagon’s joint Cyber Command said in a recent speech, “We see a disturbing track from exploitation to disruption to destruction.”
Head of NATO’s Cyber Defense Section stated that 100 countries have acquired cyber-attack capabilities and 10-15 have advanced capacity sufficient to pose significant threat.
Media are further fueling the fire with hyped-up reports and Fright Night-worthy titles such as “U.S Defense Secretary warns of ‘Pearl Harbor’ cyber-attack by Iran”, “North Korea Improves Cyber Warfare Capacity”, “Our Cyber War with China” or “NATO considers Russia one of the key potential cyber-aggressors”.
A true fear is that once cyber warfare commences then entire infrastructures can be wiped out because many crucial control systems, such as electricity and water, are set up on some form of electronic communication network.
Still, is all of this noise necessary?
In order to figure that out, we first have to decide if we really are in the midst of cyber way, or is this only a scary bedtime story that governments tell their citizens to keep them distracted from economic and social issues.
Much of the general public does not fully understand what cyber war really means. Because it includes the harshness of the word “war” coupled with the mystifying word “cyber” people can’t help but create some catastrophic event in their minds that leaves the world in the dark ages. And all of the terrifying news stories fueled by static from the powers-that-be do nothing to truly educate people on where the truth lies.
Is a cyber war currently going on and is it as serious of a threat as a traditional war?
According to NATO Cooperative Cyber Defense Centre of Excellence, the answer is clear. They issued the Tallinn Manual, which, while not an official document, is a collection of opinions expressed by independent experts.
According to the contents of the Tallinn Manual, the major difference between espionage, fraud, hacking, and cyber war is that cyber war has to cause a loss of human life or “catastrophic damage” before it can be called a war.
Based on that definition, and that one is the best I know about, there is no real cyber war going on. Yet.
Cyber intrusions that are today happening on a consistent basis between countless nations are nothing more than new way to perform old-school border intrusions and are aimed at testing the readiness and capabilities of potential opponents.
Breaches into government systems or systems of large organizations are just intelligence gathering via the Internet. Espionage and economic espionage existed for quite some time before the Internet. While the approach might have changed, the threat is nothing new. Compared to old-time HUMINT operations, cyber-attacks are easier and safer and one may even ask why any intelligence agency wouldn’t do it?
According to Forbes, “China’s cyber campaign consists mainly of espionage aimed at stealing military secrets and intellectual property.”
Recent Guardian article titled “Militarization of Cyberspace” states “Experts estimate China has as many ‘cyber jedis’ as the US has engineers, and some of them, with backing from the state, have been systematically hacking into and stealing from governments and companies in the west, taking defense secrets, compromising computer systems, and scanning energy and water plants for potential vulnerabilities.”
Or, let’s draw some comparison with Cold War: Cold War was never declared. All official statements point that Cold War was never really a war, even though there were countless “proxy” wars causing death and destruction and there were at least 70 airplanes shot down (causing hundreds of deaths) while “participating” in Cold War. (not counting those shot down during declared or undeclared conflicts or over war zones).
In last few years there were few very public cyber incidents of national level such as:
- Massive cyber operations against Estonia in 2007 by Russian efforts. This included spamming influential portals such as the Estonian Reform Party and denying the general public access to certain websites.
- Russia had another experience with cyber operations during its war with Georgia. One strategy used was intelligence scouring Georgian databases for information about their military and top secret operations.
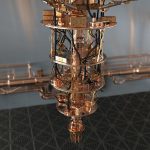
- Stuxnet penetration of Iran’s Bushehr nuclear power facility that occurred in 2010.
So far, “catastrophic damage” or loss of life has not been the outcome of current “cyber spats” between countries. There have not been countless deaths or a drastic impact on national sovereignty as we usually see with war. These incidents thus far have fallen under the classification of hacking and cyber espionage rather than a total outbreak of the predicted cyber war.
Based on all this, I wouldn’t call cyber war a “war” yet.
The Internet plays host to cyber espionage, range of cyber crimes, and a platform for activist groups to dabble with cyber terrorism, and some believe that these offenses act only as building blocks to a total cyber war. While the impacts have not been on the “war” scale yet, the possibility is certainly there and this is the struggle that people have with labeling cyber war as a true threat.
Preparation for cyber war is certainly prudent.
In response to these new cyber threats there has been a notable strengthening of information defenses around the world.
US has embarked on a crusade of infrastructure protection. The US has categorized cyber attacks as “one of the most serious national security, public safety, and economic challenges we face as a nation.” and it has recently established the U.S. Cyber Command. In 2012 the US Department of Defense issued its Strategy for Operating in Cyberspace, which designates cyberspace as an actual operational domain.
The UK has also begun working to develop defensive and offensive strategies. In 2010 UK National Security Strategy characterized “cyber attacks” as “tier one” threat to British national security.
Likewise, Canada launched Cyber Security Strategies and Russia has recently implemented cyber concepts for armed forces. China is already the big bully in cyberspace. Iran allegedly invested $1B recently to strengthen their cyber warfare capabilities. And Pakistan is building up their cyber “army”
Apparently, everyone sees the importance of having a plan…just in case.
This seems to be an adequate response since countries are growing and producing their ability to be powerhouse contenders in the event of a cyber war. Some focus on this issue is absolutely necessary, but a constant exchange of vague future-predicting does nothing to really combat this issue.
While politicians and journalists keep predicting fire and brimstone, the reality looks like the cyber war is still firmly focused on espionage, posturing and IP theft and there’s no real war going on. But, you can bet that all sides are developing more potential weapons every day and stockpiling them like the Cold War nuclear missiles.
Preparation through knowledge is beneficial, but pointless scaremongering is anything but.
For over 30 years, Marin Ivezic has been protecting people, critical infrastructure, enterprises, and the environment against cyber-caused physical damage. He brings together cybersecurity, cyber-physical systems security, operational resilience, and safety approaches to comprehensively address such cyber-kinetic risk.
Marin leads Industrial and IoT Security and 5G Security at PwC. Previously he held multiple interim CISO and technology leadership roles in Global 2000 companies. He advised over a dozen countries on national-level cybersecurity strategies.