Zigbee technology introduction
Zigbee is wireless PAN (Personal Area Network) technology developed to support automation, machine-to-machine communication, remote control and monitoring of IoT devices. It evolved from IEEE 802.15.4 wireless standard and supported by the ZigBee Alliance.
IEEE 802.15.4 standard determines specifications for the physical and data link layer and Zigbee Alliance provides standards from network layer to application layer. While Zigbee determines the contents of the transmitted message, the 802.15.4 standard provides details about the robust radio communication and medium access control.
The Zigbee Alliance, as a non-profit association, develops open global Zigbee standard for use in the Internet of Things consumer, commercial and industrial applications. It includes companies like Amazon, Samsung, Huawei, Qualcomm, Toshiba, Silicon Labs, Philips etc. Today, Zigbee 3.0 is one of the most common wireless standards implemented in IoT devices and supported in popular products such as Samsung Smart Things and Philips Hue. Zigbee Alliance improves Zigbee standard, enables interoperability among the wide range of smart devices and provides end-users access to innovative products and services, that will work together seamlessly. This alliance is responsible for certification of Zigbee devices and maintaining a list of certified products.
The most important Zigbee technology characteristics are:
- Low power consumption.
- Long battery life.
- Data-rates ~ 250 Kbps.
- Built in security.
- Built-in support for mesh networking.
- Cross-band communication across 2.4GHz and sub-GHz bands with multi PHY support.
- Global operation in the 2.4GHz frequency band according to IEEE 802.15.4 protocol.
- Regional operation in the 915Mhz and 868Mhz frequency bands.
- Sub-GHz channels transmission ranges up to 1km.
- IP Compatibility.
- Different manufacturers interoperability.
- Power saving mechanisms for devices.
Some interesting Zigbee products are:
- Speakers with a built-in Zigbee hub, as good foundation for a smart home. In addition, applications on phone or tablet can be used to add, group and manage Zigbee devices, customize routines and then activate them using voice commands.
- SmartThings Hub will work with a growing range of lighting, heating and security products, smart TVs or other home appliances, including voice control.
- Smart bulbs with Zigbee modules are always affordable and effective way into smart lighting.
- Smart contact sensors can be stick on doors or windows to provide lights and notifications as soon as they are opened. Smart contact sensors are usually easy to mount and supported by easily replaceable long-life batteries.
- Smart Zigbee plugs work in a Zigbee network. They can be connected directly to an Echo Plus, Hue bridge or SmartThings hub and control whatever device you plug into it, which makes them simple plug and play solution for electric heaters, coffee machines or standard lamps.
Zigbee protocol stack
The Zigbee protocol stack consists of four layers – Physical (PHY) layer, Medium access control (MAC) layer, Network (NWK) layer and Application (APL) layer – as shown in Figure 1. The Physical and MAC layers are determined by IEEE 802.15.4 standard. The Network and Application layers are governed by the Zigbee standard (https://research.kudelskisecurity.com/2017/11/01/zigbee-security-basics-part-1/).
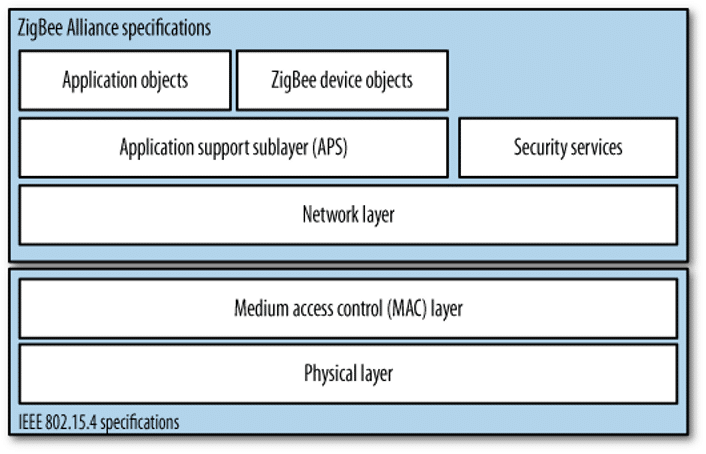
- Physical (PHY) Layer operates in frequency bands 868/915 MHz and 2.4 GHz. It is responsible for packet generation and reception, data transparency, and power management.
- Medium Access Control (MAC) Layer responsibilities include controlling radio access via CSMA-CA mechanism, beacon transmission, synchronization, and reliable radio link establishment and maintenance. There are four types of MAC frames: data frames, beacon frames, acknowledgment frames, and MAC command frames. This layer’s security is based on the IEEE 802.15.4 standard, extended with CCM mode to provide encryption and integrity protection. CCM mode – Counter with CBC-MAC (Cipher Block Chaining -Message Authentication Code) is a mode of operation for cryptographic block cyphers. It is an authenticated encryption algorithm designed to provide both authentication and confidentiality, for block ciphers with a block length of 128 bits.
- Network (NWK) Layer ensures correct operation of the IEEE 802.15.4-2003 MAC sub-layer and provides an appropriate service interface to the Application layer. It interfaces with application layer via:
- Data entity – Network Layer Data Entity (NLDE) generates network level Packet Data Units (PDU), provides topology-specific routing and security.
- Management entity – Network Layer Management Entity (NLME) configures a new device, starts a network, performs joining, rejoining and leaving a network functionality, provides addressing capabilities, neighbor discovery, route discovery, reception control and routing.
The NWK layer is responsible for the processing steps needed to securely transmit outgoing frames and securely receive incoming frames. The NWK layer’s frame-protection mechanism uses the Advanced Encryption Standard (AES) and CCM mode for authentication and confidentiality.
- The Application layer (APL) consists of Zigbee Device Objects (ZDOs), Application support sub-layer (APS), and the Application Framework.
- Zigbee Device Object (ZDO) is responsible for Zigbee End Devices, Zigbee Routers, and Zigbee Coordinators implementation. ZDO acts as an interface between the application objects, the device profile, and the applications. It assembles configuration information from the end APS to determine and implement device and service discovery, security management (key loading, key establishment, key transport and authentication), network management (network discovery, leaving/joining a network, resetting a network connection and creating a network), binding, node, and group management. Zigbee Device Object manages the security policies and the security configuration of a device. It defines three types of logical devices in a network (Coordinator, Router and End device), each having a specific role.
- The Application Support Sublayer (APS) provides an interface between the NWK and APL layer. It provides services for the establishment and maintenance of security relationships. Services are provided via APS Data Entity (APSDE) and APS Management Entity (APMSE). APSDE is responsible for data transmission services between application entities, while APMSE provides security services, binding of devices and group management. The APS sublayer allows frame security to be based on link keys or the network key. It is also responsible for the processing steps needed to securely transmit outgoing frames, securely receive incoming frames, and securely establish and manage cryptographic keys.
- Application Framework is the environment in which application objects are hosted. These are usually manufacturer defined application objects. It defines application clusters and profiles (agreements for messages, message formats, and processing actions that enable developers to create an interoperable, distributed application employing application entities that reside on separate devices).
Zigbee network logical devices
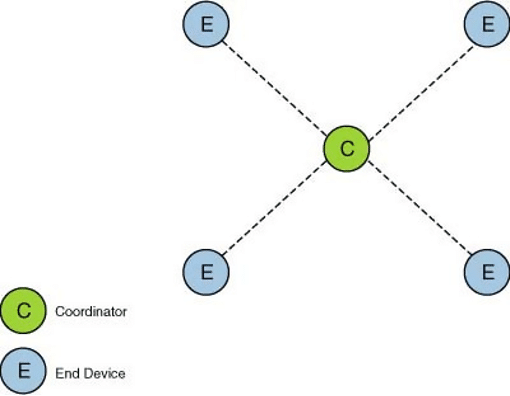
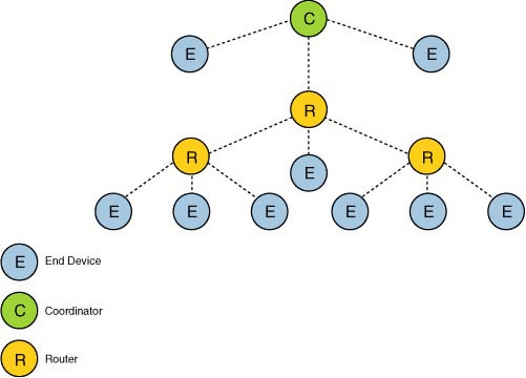
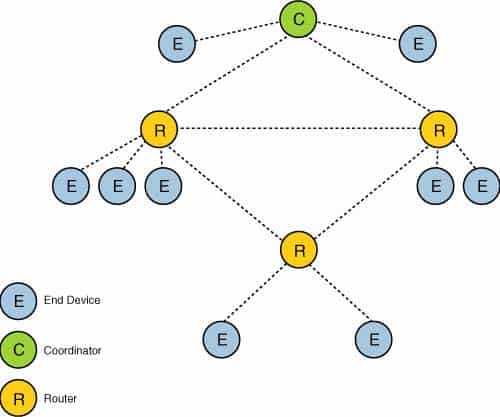
There are three types of logical devices in a Zigbee network. They are defined by the ZDO and illustrated in Figure 2.
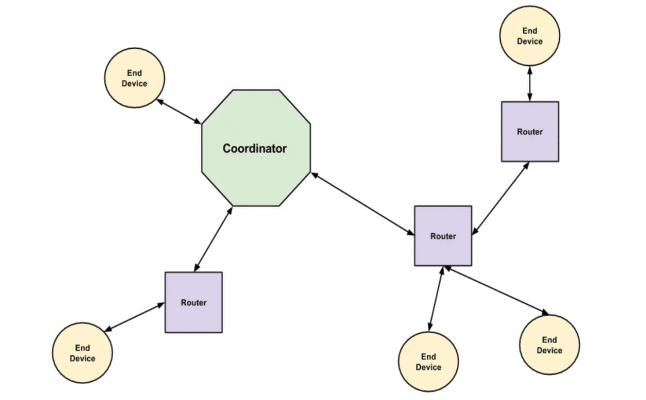
- Zigbee Coordinator is a device responsible for establishing, executing, and managing the overall Zigbee network. It is responsible for configuring the security level of the network and configuring the address of the Trust Center (the default value of this address is the Zigbee coordinator’s own address, otherwise the Zigbee coordinator may designate an alternate Trust Center). The Zigbee coordinator maintains a list of devices associated to the network. It provides support to orphan scan (devices need to verify they still have a valid Coordinator) and rejoin-processing to enable previously associated devices to rejoin the network.
There is only one coordinator per network and it can never be put to sleep. The Zigbee Coordinator is required to allow nodes to join or leave the network, as it contains the Trust Center. The Trust Center decides if a node will join a Zigbee network. Zigbee Trust Center is an application that runs on the device trusted by other devices within the network, to distribute keys for the purpose of network and end-to-end application configuration management. All members of the network recognize exactly one Trust Center in each secure network.
It is configured to operate in either standard or high security mode and may be used to help establish end-to-end application keys either by sending out link keys directly or by sending out master keys.
Standard mode is designed for residential applications. In this mode, the Trust Center maintains a list of devices, master keys, link keys and network keys with all the devices in the network. It maintains a standard network key and controls policies of network access. In this mode, each device that joins the network securely shall either have a global link key or a unique link key, depending upon the used application. It is required that Trust Center have prior knowledge of the link key value and the key type (global or unique), in order to securely join the device to the network.
High security mode is designed for high security commercial applications. Trust Center also manages the implementation of key establishment, using Symmetric-key Key Establishment (SKKE) protocol and entity authentication.
- Zigbee Router is an intermediate node device responsible for routing packets between end devices or between an end device and the coordinator. Routers need the Trust Center’s permission to join the network if security is enabled on the network. At certain occasions, routers can allow other routers and end devices to join the network. They will also maintain a list of currently associated devices, facilitate support of orphan scan and rejoin processing. Since routers link multiple sections of a network, they cannot be put to sleep.
- Zigbee End Device is usually a sensor node that monitors and collects required data. End devices are low powered or battery operated, unlike routers or coordinators. Hence, they can be put to sleep for a certain period of time to conserve energy when there is no activity to be monitored. End devices can neither route traffic nor permit other nodes to join the network.
Zigbee network topology
Zigbee networks support three types of personal area network (PAN) topologies – star, tree and mesh. The topology selection must be taken into account in the planning phase of the network and coordinated with the purpose of the network. The choice of topology is also influenced by power supply solutions of devices, their expected battery lifetime, network traffic intensity, latency requirements, the costs of network elements, etc.
Available Zigbee topologies are:
- Star topology, as presented in Figure 3, has no routers and the coordinator (data collector) is responsible for routing the packets in the network, initiating and maintaining the devices in the network. End devices can communicate only via the coordinator. Star topology weakness is a single point of failure. Failure of the coordinator can shut-down the whole network. Furthermore, the star hub can become bottleneck with network bandwidth.
- Tree topology is illustrated in Figure 4. The coordinator acts as the root node responsible for establishing the network and choosing certain key network parameters. A router can be a child to the coordinator or another router and is responsible for moving data and control messages through the network, using hierarchical routing strategy. An end device can be a child to a coordinator or a router and can communicate to another end device only via a router or a coordinator. Tree networks may deploy beacon-oriented communication as per the IEEE 802.15.4 standard. Tree topology weakness is that children nodes could become unreachable if their parent node shuts-down.
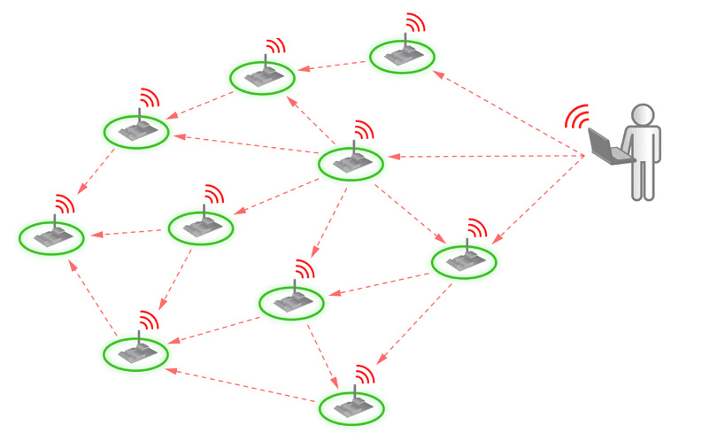
- Mesh topology is presented in Figure 5. It allows full peer-to-peer communication. It has a single coordinator, multiple routers to extend the network, and optional end devices. The coordinator is responsible for establishing the network and choosing certain key network parameters. In this topology, routers cannot transmit beacons. The failure of a coordinator does not result in a single point of failure. Complexity and difficulty to setup and maintain are main mesh topology weaknesses.
Zigbee Security
Zigbee is considered to be a secure wireless communication protocol, with security architecture built in accordance with IEEE 802.15.4 standard. Security services provided by Zigbee include key establishment, key transportation and frame protection via symmetric cryptography. However, Zigbee security features are based on certain assumptions:
- Zigbee assumes an “open trust” model. The protocol stack layers trust each other. The layer that originates a frame is responsible for its security.
- The security services cryptographically protect the interfaces between different devices only.
- Interfaces between different stack layers in the same device are arranged non-cryptographically.
- The secret keys are not discovered during key-transport. An exception to this is during pre-configuration of a new device, in which a single key may be sent unprotected.
- Availability of almost perfect random number generators.
- Availability of tamper-resistant hardware.
Taking into account the above mentioned assumptions, in this chapter are discussed some important security features (different security models, key types and keys management) provided by the Zigbee standard.
Zigbee security models
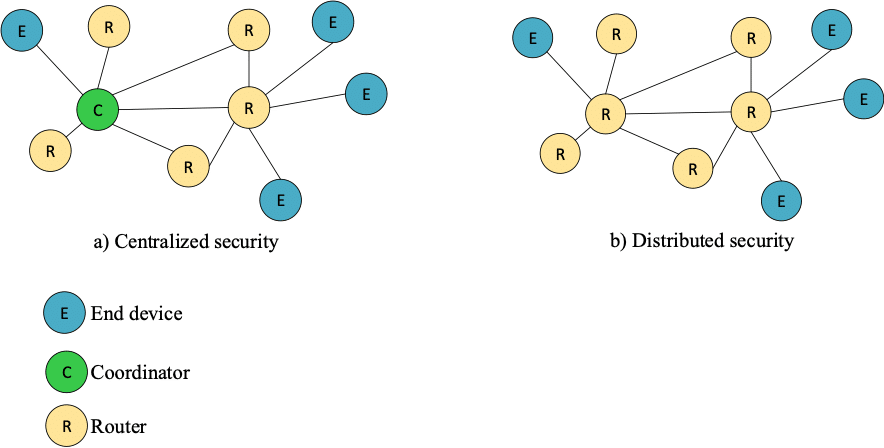
There are two types of security models in Zigbee networks, as presented in Figure 6. They mainly differ according to the implemented mechanism, how new devices are admitted into the network and how they protect the messages in the network – Centralized security network and Distributed security network.
- Centralized Security model is complex but more secure and involves the Trust Center (network coordinator). Only Zigbee Coordinators with Trust Center can establish centralized networks. Nodes join the network, receive the network key and establish unique link key with Trust Center. The Trust Center is responsible for:
- Configuring and authenticating routers and end devices that join the network.
- Generating network key to be used for encrypted communication across the network.
- Periodically or as required, switching to a new network key, as a security protection method. If an attacker acquires a network key, it will have a limited lifetime.
- Establishing a unique link key for each device, as they join the network.
- Maintaining the overall security of the network.
- Distributed security model is simple, but less secure. This model supports only routers and end devices. Routers find their role in formatting the distributed network and they are responsible for sign up of other routers and end devices. Routers publish network keys (used to encrypt messages) to newly joined routers and end-devices. All the nodes in the network use the same network key for encrypting messages. Also, all nodes are pre-configured with a link key (used to encrypt the network key) before entering the network, as there is no Coordinator and Trust Center.
Zigbee security keys
There are three types of 128-bit symmetric keys determined by the Zigbee standard:
- Network key is used in broadcast communication. Each node requires the network key in order to communicate securely with other devices on the network. The Trust Center generates the network key and distributes it to all the devices on the network. A device on the network acquires a network key via key-transport (used to protect transported network keys) or pre-installation. There are two different types of network keys – standard (sent without encryption) and high-security (encrypted network key).
- Link key is used in unicast communication. A device acquires link keys either via key-transport (key-load key is used to protect transported link keys), key-establishment (specific key-establishment procedure is initiated based on device security profile), or pre-installation (for example, during factory installation). This key provides APL level security in addition to NWK level security provided by the network key. Messages between the nodes are encrypted with both – network and link keys.
Zigbee defines two types of link keys – global and unique. Global link keys are established between the Trust Center and the device. Usually, link keys related to the Trust Center are pre-configured using an out-of-band method, for instance QR code in the packaging. Unique or application link keys are established between two devices in the network, without Trust Center. Both types of keys may be used in the network, but a device shall only have one type in use. The type of link key determines how the device handles various Trust Center messages (APS commands), including APS encryption.
Furthermore, each node may also have the following pre-configured link keys which would be used to derive a Trust Center link key:
-
- A default global Trust Center link key defined by the Zigbee Alliance has a default value. It is used or supported by the device, if no other link key is specified by the application at the time of joining.
- A distributed security global link key is a manufacturer specific key used for interaction between devices from the same manufacturer.
- Install code is a preconfigured link key. All Zigbee devices can contain a unique install code, a random 128-bit number protected by a 16-bit cyclic redundancy check (CRC). The Trust Center may require that each new device use a unique Install code to join a centralized security network and the Install code must match a code previously entered into the Trust Center. Once the Install code is verified, the joining device and the Trust Center derive a unique 128-bit Trust Center Link Key from the Install code using the Matyas-Meyer-Oseas (MMO) hash function.
- Touchlink preconfigured link key – is used for devices that will join a network using the Touchlink commissioning procedure.
- Master key forms the basis for long-term security between two devices. Its function is to keep the link key exchange confidential between two nodes in the SKKE protocol. A device acquires a master key via key-transport, pre-installation or user-entered data such as PIN or password.
Key management
Zigbee supports different key management mechanisms:
- Pre-installation – the manufacturer installs the key into the device. If there are several keys preinstalled in the device, the customer can select one of the installed keys by using a series of jumpers in the device.
- Key establishment method of generating link keys based on the master key. Different security services of the Zigbee Network use a key derived from a one-way function (with link key as the input) to avoid security leaks due to unwanted interactions between the services. This key-establishment is based on the SKKE protocol. The devices involved in communication must be in possession of the master key, which may have been obtained through pre-installation, key transport or user-input.
- Key transport – the network device makes a request to the Trust Centre for a key. This method is valid for requesting any of the three types of key in commercial mode, whereas in residential mode the Trust Centre holds only the network key. The key-load key is used by the Trust Center to protect the transport of the master key.
Additionally, in the centralized model, keys can be distributed using Certificate-Based Key Establishment protocol (CBKE). CBKE provides a mechanism to negotiate symmetric keys with the Trust Center based on a certificate stored in devices at manufacturing time and signed by a Certificate Authority (CA).
Zigbee Security Strengths
The Zigbee Alliance and its members are continuously improving security performances of Zigbee technology, to achieve optimal balance between deployment, exploitation and security requirements in wireless machine to machine communication.
To meet the security needs, Zigbee provides a standardized set of security specifications based on a 128-bit AES algorithm and compatible to wireless 802.15.4 standard. In Zigbee networks security is defined for the MAC, NWK and APL layers. Security mechanisms include key establishment and transport, device authorization and frame protection.
The MAC layer controls access to the shared medium and manages single-hop transmissions between neighboring devices. The Zigbee Alliance added a NWK layer security option to extend some security functionalities not available at the MAC layer (capability to reject expired data frames).
It is very important to choose an optimal place to apply security mechanisms. If the application needs strong security, then APL layer would be the choice. This approach protects against both internal and external attacks, but it requires more memory to implement.
Some representative security mechanisms, supported by Zigbee standard are:
- Encryption with AES-CCM provides data confidentiality, authentication and integrity. Encryption and integrity protection prevents an eavesdropper from being able to interpret frame payload. Integrity protection adds a Message Integrity Code (MIC) to be transported along with the data to be protected. The MIC “signs” the data and allows the recipient to verify that the data has not been tampered. The MIC is also connected to the identity of the originator and thus provides origin authenticity.
- Replay protection – each node in the Zigbee network contains a frame counter that is incremented at every packet transmission. Each node also monitors the previous frame counter values of devices that is connected to. If a node receives a packet from a neighboring node with the same or lower frame counter value than it had previously received, the packet is dropped. This mechanism enables replay protection by tracking packets and dropping them, if they were already received by the node. The only time the frame counter is reset to 0 is when the network key is updated.
- Device authentication is procedure of confirming a new device, that joins the network as authentic. The new device must be able to receive a network key and set proper attributes within a given time frame to be considered authenticated. Device authentication is performed by the Trust Center. There are two Trust Center authentication modes available – residential and commercial. Residential mode is lightweight, but it doesn’t establish keys or scale with the size of the network. Commercial mode establishes and maintains keys and scales well, but requires memory resources.
In residential mode, if the new device already has the network key, it must wait to receive a dummy (all-zero) network key from the Trust Center as part of authentication procedure. At the moment of joining the network, the new device does not know the address of the Trust Center and uses the source address of received message from Trust Center to set this address. If the new device that joins the network does not have a network key, the Trust Center sends it.
In commercial mode the Trust Center never sends the network key to the new device over an unprotected link. However, the master key may be sent unsecured in commercial mode, if the new device does not have a shared master key with the Trust Center. After the new device receives the master key, the Trust Center and the new device start the key establishment protocol (SKKE). The new device has a limited time to establish a link key with the Trust Center. If the new device cannot complete the key establishment before the end of the timeout period, the new device must leave the network and retry the association and authentication procedure. When the new link key is confirmed, the Trust Center will send the network key to the new device over a secured connection.
Furthermore, Zigbee also supports device-unique authentication at joining the network – such as Touchlink commissioning, which is an easy to use proximity mechanism for commissioning a device into a network.
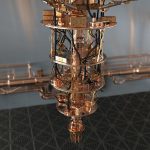
- Secure over-the-air (OTA) firmware upgrades, presented in Figure 7, allow a manufacturer to add new features, fix defects in end device, and apply security patches as new threats are identified.
Once a device receives an encrypted data, during an OTA upgrade, it decrypts, validates the signature, and then updates the device. Furthermore, the validity of the active image is checked each time the device boots. If the image is invalid, procedure prevents it from updating and returns to using the last one.
- Logical link-based encryption is the ability to create an application level secured link between a pair of devices in the network. This is managed by establishing a unique set of AES-128 encryption keys between a pair of devices.
- Runtime key updates can be performed periodically or as required. The Trust Center is responsible for changing the network key. It generates a new network key and distributes it throughout the network by encrypting it with the old network key. All devices continue to retain the old network key for a short period of time after the update until every device on the network has switched to the new network key. Also, after receiving the new network key, the devices initialize their frame counter to zero.
- Network interference protection – in low-cost Zigbee nodes, using a band-select filter is not an available option, due to cost or node size limitations to protect the network from interference. However, basic properties of IEEE 802.15.4 and Zigbee network, such as low RF transmission power, low duty cycle, and the CSMA/CA channel access mechanism help reduce a Zigbee wireless network influence on interference. There are two methods for improving the coexistence performance of Zigbee networks: collaborative and non-collaborative.
In collaborative methods, certain operations of the Zigbee network and the other network are correlated and managed together. To avoid packet collisions, every time one network is active, the other network stays passive. In this method, there must be a communication link between the Zigbee and the other network.
The non-collaborative methods are the procedures that any Zigbee network can follow to improve its coexistence performance, without any knowledge regarding the nearby interfering wireless devices. This method is based on detecting and estimating interferences and avoiding them whenever possible.
Some of the non-collaborative methods applicable to Zigbee wireless networking include:
-
-
- Carrier Sense Multiple Access with Collision Avoidance (CSMA/CA) – is a media access protocol, where node verifies absence of other traffic and checks if the channel is sensed to be “idle” before transmitting.
- Spread spectrum technologies support improves the network robustness against interferers – such as Direct Sequence Spread Spectrum (DSSS).
- Dynamic RF output power control adjusts the transmitted RF output power based on the channel condition and the distance of the receiving nodes.
- Mesh networking and location-aware routing support network in finding alternative routes to the final destination and avoiding routers and nodes close to interference source.
- Frequency channel selection is capability to change the frequency channel when the level of the interferer signal is unacceptable. Zigbee supports frequency agility – capability that allows the entire network to change channels in the presence of interference.
- Adaptive packet length selection is correlated to radio propagation conditions. Reducing the size of the packet is normally considered a way of improving the error rates in poor propagation conditions. Smaller packets are generally more suitable for transmission and reception.
-
Zigbee Security Weaknesses
Zigbee has some security vulnerabilities, which makes it similar to other wireless technologies. Zigbee networks implementation has to be performed taking into account possible security threats. Security attacks and unauthorized usage are quite possible, as Zigbee technology is applicable to remote control and monitoring of sensitive resources, infrastructure or home security.
Some important security issues in Zigbee networks would be:
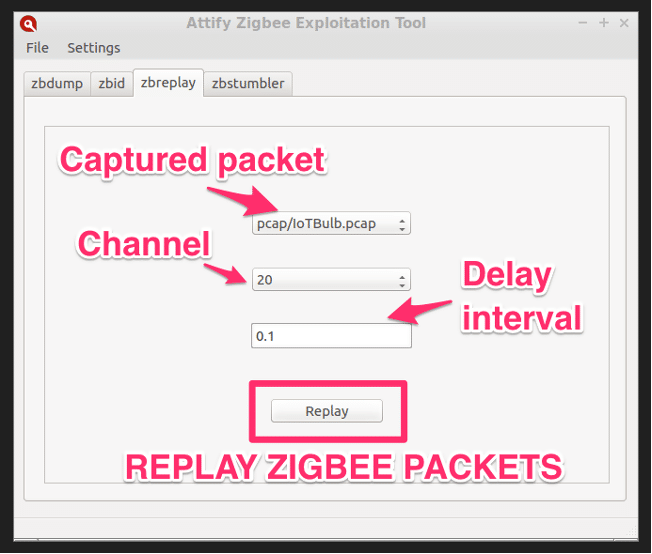
- Replay and injection attacks goal is to trick Zigbee devices. In the first phase, some tools for Zigbee network discovery transmit beacon request frames and analyze responded information about the available nodes in the network. This entire process finds Zigbee devices working on dedicated working channels, sends and receives beacon request and response frames over that single channel. Next phase is capturing the packets, analyzing them and then replaying the same packets to cause a change in the behavior of the device, determined by the replayed packets. Hence, captured packets from Zigbee nodes are sent back in a replay attack scenario, to make it look as they came from the originating node. The network will treat the malicious traffic as regular. An example of Zigbee software pen-testing tool for replay attacks is presented in Figure 8.
- There are several other attacks that accompany replay attack – just as an example is a malicious user that receives packets at one point in the network and then replays these packets in other areas to interfere with the overall network functionality (wormhole attack).
- In residential mode, if the new device that joins the network does not have a network key, the Trust Center sends the network key over an unprotected link and makes the network vulnerable.
- Misplace of some low-cost Zigbee devices with limited protection capabilities – without tamper-resistance (such as temperature sensors and light switches), introduce opportunity for an unauthorized person to enter the door with privileged information – keys, network identification, working channels etc.
- For the purpose of achieving and maintaining device interoperability, Zigbee uses the same security level for all devices on a given network. It could lead certainly to some security risks. Hence, the responsibility is in developer hands to address these issues and include policies to detect and handle errors, loss of key synchronization, periodically update keys, etc.
- OTA firmware upgrade is typically applied to sophisticated Zigbee networks to ensure better security and updates. Security protection during OTA procedures can be bypassed using a device that mimics the Zigbee node and selects the transmission that is exchanged between the network devices. These packages can later be analyzed or decrypted. Some combined hardware and software tools are capable to effectively intercept and analyze 802.15.4 packages. This kind of attack is very hard to discover.
- At the MAC layer, if an attacker floods a channel with frames, network will be forced to deny any communication between devices. This is realistic scenario because Zigbee uses CSMA/CA mechanism (if it is running in non-beacon mode) and devices always check if a channel is busy before transmission, thereby resulting in an DDoS attack.
- Reusing Initialization Vector (IV) value with the same key is a security vulnerability inherited by Zigbee from 802.15.4. It enables an attacker to recover two plaintexts using their cipher-texts. Recovering the two plaintexts is a simple XOR operation on the two cipher-texts, encrypted with the same keys and IV – same nonce value. This attack is known as the same-nonce attack.
- Without integrity protection provided by Message Integrity Code, a rogue device could modify a transmitted frame and the modification may not be detected by the recipient.
- Unauthenticated acknowledgement packets (ACK) could influence security in Zigbee networks. The 802.15.4 and Zigbee specification does not provide integrity and confidentiality protection for acknowledgment packets. Hence, an unauthenticated remote attacker can spoof acknowledgement packets. This threat is a direct consequence of man-in-the-middle attack.
- A denial-of-service (DoS) attack causes a node to reject all received messages. In a Zigbee network, DoS can be achieved by altering routing tables to redirect all or some of the network traffic to a malicious device (sinkhole attack). It can be done by purposely sending messages to build artificial routing paths or to implement loops to the routing process of legitimate nodes. As a consequence, transmission of packets among devices is hampered.
- In Zigbee specification, the frame counter is referenced as a security measure. It rejects frames that have been replayed. The counter will normally reset if a new key is created. The sequential freshness is used in this context to prevent malicious attacks. However, this protection has some weaknesses – as the frame counter uses incrementing values rather than random, an adversary can choose great values to avoid the rejection of specific frames. It is also easy to overflow the frame counters. An attacker might cause rejection of further frames and produce a DoS attack in the network, simply by transmitting a frame with the maximum possible value. This attack is possible in situations where MIC of the packet is not verified.
- DoS attacks could be realized too, by using jamming techniques to trick the user for initiation of a factory reset and preventing the devices from communicating. It could be also realized by sending a “reset to factory default” command to the device and wait on the device to look for another Zigbee network to connect.
- Touchlink procedure initiator has capability to send a factory-reset command to a target node in the network, allowing the target node to be removed from the current network and entered to another one. This procedure can be misused and malicious attack can be realized to exclude node(s) from the network. It can be serious threat for some protection and security systems.
- Forward security requirement has to be addressed properly. Upon leaving the network, a node is still able to access the communication, since it still possesses the master and link keys. If we analyze an example of a corporation using Zigbee devices for opening doors or improving energy efficiency, it is not impossible that one or many of the devices are lost or stolen. For that reason, if the keys stored on the devices are not properly revoked, someone might take advantage of the situation and exploit this weakness. Therefore, this type of attacks together with network physical security should not be underestimated and must be taken seriously.
Conclusion
In order to meet the increased system requirements, the Zigbee Alliance is permanently engaged in security improvements (new algorithms and functions research and development, security protocols and hardware and software support requirements, networks and system organization and settings, regulatory topics and standards establishment). It can be said that the AES algorithm provides robust encryption to Zigbee standard. In addition, the overall system security depends on the encryption keys (their initialization, production, exchange) and specifically tailored network design, deployment, management and maintenance. As the conclusion, connectivity of Zigbee network can contribute to the quality of the modern life communications and fulfillment of consumers’ expectations from IoT world, only if established with security preferences.
For over 30 years, Marin Ivezic has been protecting people, critical infrastructure, enterprises, and the environment against cyber-caused physical damage. He brings together cybersecurity, cyber-physical systems security, operational resilience, and safety approaches to comprehensively address such cyber-kinetic risk.
Marin leads Industrial and IoT Security and 5G Security at PwC. Previously he held multiple interim CISO and technology leadership roles in Global 2000 companies. He advised over a dozen countries on national-level cybersecurity strategies.