In their growing efforts to increase efficiencies through digitization and automation, railways are becoming increasingly vulnerable to cyber-kinetic attacks as they move away from strictly mechanical systems and bespoke standalone systems to digital, open-platform, standardized equipment built using Commercial Off the Shelf (COTS) components.
In addition, the increasing use of networked control and automation systems enable remote access of public and private networks. Finally, the large geographical spread of railway systems, involving multiple providers and even multiple countries, and the vast number of people involved in operating and maintaining those widespread systems offer attackers an almost unlimited number of attack vectors. Railway systems are rampant with cyber-kinetic vulnerabilities.
Railways at cyber-kinetic risk
My team performed a comprehensive assessment for a rail provider in a middle of a large digitization project. The bottom line was that we found more than 20 cyber and intentional electromagnetic interference (IEMI) ways to cause kinetic impacts that would either lead to application of emergency breaks, derailment or a crash.
Other researchers’ three-year security assessment of a wider scope of railway systems have found some glaring poor practices in some systems’ security. These failures include:
- Continued use of obsolete software whose manufacturers no longer provide patches for discovered security vulnerabilities
- Hard-coded passwords for remote access
- Networks that housed both engineering systems and easy-to-access passenger entertainment systems, making it possible to hack into operations equipment through the passenger systems
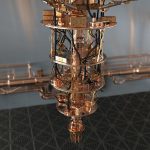
Another study revealed other common vulnerabilities. It showed that one type of programmable logic controller (PLC) that is known to be vulnerable to cyberattacks is commonly used by rail systems across Europe. Furthermore, GSM-R SIM cards commonly used for communication with trains in some countries could be compromised by GSM jamming or hijacked by a skilled attacker through their OTA (over-the-air) firmware update function.
Clearly, vulnerabilities abound. But what is even more shocking is to find how aware potential attackers are of those vulnerabilities.
“Project HoneyTrain”
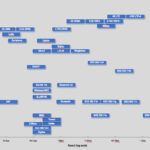
In 2015, automation experts Koramis GmbH and security experts Sophos joined in a project to help them learn what railway systems were up against in terms of the skill level, methods and apparent motives of potential cyberattackers of mass transit and rail systems. They created a simulated rail infrastructure that they called “Project HoneyTrain” that would look like a real railway to online attackers. The project was online for six weeks, so that researchers could learn, record and analyze attacks.
This system simulated much more than just the digital systems of a rail system. To someone hacking it, it was indistinguishable from a real rail system, all the way down to closed circuit TV feeds from the supposed train operator cabins, working control interfaces that attackers could access and websites that offered real-time schedules and statuses of trains. This system was intentionally left with security protections that used some of poor practices found in real rail systems to see how attackers would respond.
Results were jaw-dropping. In those mere six weeks, 2,745,267 attacks were recorded. Approximately 10% of them reached industrial components and four valid login attempts enabled access to human machine interface (HMI), through which the attackers were able to gain limited control of the virtual trains, but not control them to the point where serious damage would have occurred had the trains been real. There was also evidence that once HMI was breached, attackers later returned to try to penetrate deeper into the systems.
Overall, the sequence of attacks showed the researchers “… that the attacker has a deep knowledge of the industrial control systems used for our HoneyTrain project. These actions were not performed randomly, but deliberately.” The project shows that malicious actors with knowledge of ICSes actively scan for and attempt to exploit railway infrastructure online.
The attractiveness of targeting mass transit and railway systems with cyber-kinetic attacks
Railways and metropolitan mass transit are prime targets for terrorists. Causing death or injury to a large number of people traveling by rail would make just the kind of impact terrorists seek.
Freight train transit is also an attractive target for terrorists. A large train derailment can take days to clear. It blocks not only the rail line, but also intersecting roadways.
Railways are also the preferred transportation mode for hazardous materials. So, from terrorist’s point of view, derailment of such materials can potentially multiply impact of an attack. Release of hazardous materials can force nearby residents to evacuate their homes and cause long-term damage to the environment.
With both people and goods being highly dependent on rail transport, disruption to it would have huge economic impact. The U.S. Department of Transportation Federal Railroad Administration quotes a 2012 report that states:
“Since each person in the U.S. requires the movement of approximately 40 tons of freight every year (emphasis added), many of the goods people use daily are either wholly shipped or contain components shipped by rail. Of rail freight, 91 percent are bulk commodities, such as agriculture and energy products, automobiles and components, construction materials, chemicals, coal, equipment, food, metals, minerals, and paper and pulp. The remaining 9 percent is intermodal traffic which generally consists of consumer goods and other miscellaneous products.”
How attractive are rail systems to terrorists? Rail systems are so attractive that Al Qaeda published detailed information in its online magazine for sympathizers instructions for how to construct an untraceable tool to derail trains, and the best rail lines to target in the U.S. and Europe. And they have proven their willingness to target rail systems. They were the group responsible for the 2004 Madrid railway bombings that killed 191 people and wounded more than 1,800.
Railways are also attractive to criminals because of the economic impact. Their goal is not to harm people, but to extort municipalities into paying ransom to release compromised mass transit systems from their control. Ransomware attacks like this have already occurred against the San Francisco Muni system in November of 2016 and the Deutsche Bahn German railway system in 2017.
Railway systems would offer attackers a wide range of targets even if they weren’t connected to the cyberworld: a multitude of stations, signaling systems and miles of tracks, often in remote areas, make securing everything highly challenging. Urban transit stations move hundreds of thousands of passengers through crowded concourses every day and have already attracted attackers in London, Russia, Belgium, Turkey and India in recent years.
Add to that the increased vulnerabilities that arise through the rapid digital transformation of the industry, and the potential attack footprint grows even larger. Digital vulnerabilities pose a painful conundrum for the rail industry, as Waterfall Security’s CEO and co-founder Lior Frenkel describes:
“The biggest risk to industrial networks occurs when there is a connection to an external network. In many ways, connecting rail systems to the internet is quite reckless, but delivers so many efficiencies that it’s hard to see a day when public transport won’t be connected. What is most concerning is when the mission-critical control systems are connected to the same networks used by the passengers or the business networks. Here you open up the control system to the bad guys, who needn’t even be on-board the train to find a way into the control system.”
Known railway system cyberattacks
Known cyberattacks on railway services, so far, have caused few injuries and no deaths. Their frequency, however, has increased over the years. A growing number of what might be called “preparatory attacks” cause no immediate disruption but establish a foothold in systems for future attacks. Similarly, ransomware attacks that extort money from rail services in exchange for returning control of systems to the owners have increased. The following examples show the history of rail service cyberattacks and their developing trends.
CSX U.S. railway system
A worm that infected millions of computers in August 2003 caused nearly a day’s worth of delays along CSX’s entire East Coast rail operations. Although the attack did not target the rail system specifically, the lack of system segmentation in CSX’s systems allowed an infection in an email opened by an employee to shut down signalling, dispatching and other critical systems.
Lozd, Poland, tram hack
In 2008 a 14-year-old described by his teachers as a model student and computer genius, studied his city’s tram system for months to reverse-engineer its remote operations functions. He converted a television remote control into an infrared device that enabled him to control key points of the tram’s track switching system. Without considering the consequences, he caused four trains to derail, injuring 12 people.
Unidentified U.S. railway system
An unnamed U.S. rail service in the Pacific Northwest suffered a cyberattack in December 2011 that had a minor effect on its operations. The official investigation described the attack as part of random exploration of U.S. digital systems by overseas hackers rather than as an attack that specifically targeted that rail service.
Four cyberattacks on UK rail
Security researchers, mid-2016, uncovered at least four cyberattacks on UK rail systems over the previous year. Although the incidents did no discernible damage, they suggest that state actors were compromising systems to establish a presence in them to prepare for possible future exploitation.
San Francisco Municipal Transit System ransomware attack
A ransomware attack on the San Francisco Municipal Transit Authority (SF Muni) paralyzed the ticketing system for one day, until backed up data for those systems were installed to get the system running again. Disruptions to passengers were minimal. In fact, the transit system remained operational during the attack, giving riders free fares until the problem was resolved. SF Muni’s systematic backing up of all data and segmentation of backups from the main system enabled the fast recovery.
German railway ransomware attack
In May 2017 a ransomware attack on German railway service Deutsche Bahn disrupted service for half a day. The initial infection likely entered through an opened phishing email, but it spread further than anticipated because of unexpectedly inadequate segmentation of systems.
Critical railway systems
Railway and mass transit services rely on a multitude of critical component systems for their operations. These include communications-based train control, traction power control, emergency ventilation control, alarms and indications, fire detection systems, intrusion detection systems, train control/signaling, fare collection, automatic vehicle location, physical security camera feeds (CCTV), access control, public information systems, public address systems, and radio/wireless/related communication, to name a few.
Each system offers attackers an attractive target, and a growing number of operational systems are COTS solutions. Such generic solutions save the railway companies money compared to proprietary solutions, but often offer questionable security.
Typically, railway systems consist of a mix of old, nondigital legacy systems and newer digital ones. Obviously, nondigital systems pose no cyber-connectivity vulnerabilities and require only physical and administrative security. Digital systems may vary on the level of connectivity they possess, with greater connectivity posing greater vulnerability.
Specific cyber-kinetic security challenges in railway systems
Rail systems pose some unique security challenges. One challenge is the massive shift from mechanical to digital systems.
As tests proceed on replacing old, mechanical signaling systems across the UK with digital ones of the European Rail Traffic Management System (ERTMS), researchers warn about the possibility of cyberattacks. They express concern that rail leaders have developed a false sense of security about the changeover to digital systems, because the old mechanical systems have been so rarely compromised. Assuming that this low rate will carry over to digital systems is not realistic, though.
Mechanical systems required attackers to be physically present at a physical control point to compromise it. As digitization increases, this restriction on attackers’ location will disappear. Systems will be hackable remotely.
Adding to the difficulty in securing rail systems is the fact that they are physically spread over large geographic areas. This multiplies potential access points to systems, which increases the difficulty in securing them.
The large number of personnel needed to access and run systems adds another security challenge. Disgruntled workers, or workers who have been bribed or coerced will have access to digital input points across vast geographical areas. Each of these many input point offers opportunities to introduce malware into the system, either knowingly or accidentally.
Rail systems also share a problem common to many cyber-physical systems, especially those that are widely distributed like rail services. Maintaining the physical components of the system is critical for maintaining safety, resulting in safety personnel and security personnel having responsibility for the same systems. This opens the possibility of the two sets of personnel inadvertently working at cross purposes.
Ensuring the safety of signaling systems, for example, is crucial to preventing collisions. A physical breakdown of signaling systems is just as hazardous to safety as someone digitally altering their intended operation. Both safety and security need to be designed into systems and constantly maintained. Yet those who ensure safety of physical systems prone to wear and tear and those who ensure security of digital systems often approach those systems in completely opposite ways.
The broad geographic area that rail systems cover require safety professionals to approach them by breaking them into separate components on which they can conduct systematic, rotating checks over time. Security professionals, on the other hand, approach the system holistically, rather than by its component parts.
These different approaches hold potential that either safety or security personnel might unknowingly make changes that impair the efforts of the other. Thus, it is imperative that both work closely together to ensure that they achieve an optimal combination of security and safety.
Furthermore, while safety personnel need concern themselves only with the equipment owned by their own rail service, security needs may involve multiple stakeholders, as systems connect between those stakeholders – not to mention, at times, different countries. All connections between stakeholders need to be secured, as well as the individual systems within them. Thus, cooperation is crucial between not only different disciplines, but also a wide variety of stakeholders.
Finally, we need to add the time factor into the challenges of securing rail systems. The organizations running them are used to dealing with mechanical systems whose replacement windows are measured in decades. Incorporating digital controls into the mix changes that dynamic dramatically. The speed of digital advancement is measured in mere years. If rail organizations digitize and yet expect to maintain the same extended replacement windows, they will only increase vulnerabilities, because digital systems become obsolete much faster than mechanical ones and are prone to undiscovered vulnerabilities.
What governments and rail services are doing
Fortunately, governments and rail services are not turning a blind eye to the new vulnerabilities. Many are actively involved in developing new standards to address security needs as rail transport systems become increasingly digitized. Here are some of the efforts they are making.
UK
The Rail Safety and Standards Board (RSSB) and the UK Department for Transport have released a guideline, Rail Cyber Security Guidance to Industry to address the emerging concerns on digitized railway systems and offer high-level recommendations for enhancing security. RSSB and the UK Department for Transport also work together with The Centre for Protection of National Infrastructure (CNPI) on developing a cross-industry cybersecurity strategy for the rail industry.
In addition, the rail industry itself is looking into reducing vulnerabilities. The Rail Delivery Group, a UK rail industry body, has released its own Rail Cyber Security Strategy, that seeks to set UK railways on course of creating a culture of cybersecurity that can make UK railway cybersecurity a model for railway systems around the world.
UK railway providers have taken up this challenge, seeking to embed cybersecurity into the end-to-end systems lifecycle, and have taken a strong risk management approach, borrowing methodologies from the financial services sector to better recognize potential attack vectors. They also have focused on better managing their supply chain risk, recognizing that many successful attacks started from a third-party relationship. Finally, they lead the way among rail services in developing rapid response capabilities in case someone succeeds in defeating their preventative measures.
U.S.
The U.S. Department of Homeland Security (DHS) has issued a series of guides on railway cybersecurity standards, including Transportation Industrial Control Systems (ICS) Cybersecurity Standards Strategy in 2012, as well as Transportation Systems Sector Cybersecurity Framework Implementation Guidance in 2015. In addition, the U.S. Transportation Security Administration (TSA), which is part of DHS, developed a Surface Transportation Cybersecurity Toolkit which refers to ICS framework and guidelines from the U.S. National Institute of Standards and Technology (NIST) and includes emergency response support from the US-CERT.
TSA also added cybersecurity into its Mass Transit BASE assessment framework to help transit providers evaluate the status of their security and emergency response. Finally, DHS, together with American Public Transportation Association (APTA) and Association of American Railroads (AAR), established the Surface Transportation Information Sharing & Analysis Center (ST-ISAC) to enable sharing of incidents and suspicious patterns among surface transportation organizations. This initiative includes the Transit and Rail Intelligence Awareness Daily Report (TRIAD).
In addition, individual U.S. rail services focus on continuous assessment, monitoring and awareness. They monitor thousands of log sources and assess hundreds of millions of log events each day. Cyber intelligence is widely and frequently shared. Security staffs monitor a wide number of intelligence sources daily and keep personnel apprised of the latest attacks and techniques.
Some rail services have worked hard to bring IT and OT security staffs together into a converged body that promotes enhanced communication between the two disciplines. They also have developed dedicated security teams to give intimate attention to key areas of vulnerability, to train rank-and-file staff in vulnerabilities of which they need to be aware and to decrease response time to attacks.
Canada
Transport Canada cooperates closely with the U.S. TSA on cybersecurity guidance and frameworks, but Canadian railways share cyber threat information through the cross-industry Canadian Cyber Threat Exchange and US Surface Transportation Information Sharing and Analysis Center (ST-ISAC). Like U.S. railway services, Canadian ones focus on making staff aware of threats, attacks and new techniques. Also, like UK railway services, they have established a strong focus on standards for working with third-party technology providers, to reduce their vulnerabilities there.
France
The ANSSI (National Agency for Information System Security) has identified VIO (Vital Importance Operators), which includes also the main rail and metro operators. It also publishes step-by-step recommendations on cybersecurity. These will be formalized through laws.
EU
The European Union Agency for Network and Information Security (ENISA) published numerous guidelines. These include Cyber Security and Resilience of Intelligent Public Transport and Cybersecurity for Railway Signaling. The EU has also funded multiple public-private projects on cybersecurity of railways, such as CYRAIL (CYbersecurity in the RAILways sector); SECRET Project, to address the risks of electromagnetic interference (EMI) attacks; and ECOSSIAN (European Control System Security Incident Analysis Network), the pan-European program for detection and management of attacks on critical infrastructure.
Other EU/ENISA initiatives include CERT support for cyber incidents in railways, as well as EU-wide disaster alerting, management and exercises (including cyberattack exercises). Also, the Network and Information Security Directive (NIS) implemented into law in 2018 focuses particularly on cybersecurity of operators of essential services, including rail.
International
The International Union of Railways now includes cybercrime in their Rail High Speed Network Security Handbook.
Further steps to take
Norbert Howe, in connection with the International Railway Signal Engineers (IRSE) Technical Committee, makes the following basic suggestions that can be applied across all railway systems:
- Establish cybersecurity design principles – Develop a mindset for security within the organization and apply design rules on several levels of the system architecture.
- Create a stronger perimeter – Apply strong measures such as Security Gateways and Web Application Firewalls and VPN on the external interfaces.
- Deploy system security and detection/recovery controls – A Security Information and Event Management Solution (SIEM) and centralized antivirus platforms should be used in order to immediately alert those responsible for security.
- Meet cybersecurity standards – Follow industry best practices by implementing according to strong standards.
- Embed cybersecurity in the project life cycle – Signaling system projects have to incorporate and apply security measures during all phases – from bid to testing and putting into operation.
- Establish and perform risk assessments and penetration testing – Map the threats and vulnerabilities for each asset of the system and establish a clear view on the related cybersecurity risk. Ensure the implementation of the relevant measures and perform penetration tests in order to verify their effectiveness.
- Maintain good operational conditions – Apply and regularly check the application of clear rules and procedures in order to keep up the level of security management throughout the system lifetime, including updates and system changes.
- Mandate safety protection – Implement measures to ensure message integrity and safety control in order to safeguard the system against unauthorized messages and malicious software.
The following list provides a brief summary of the most common initiatives I end up advising my railway clients for securing railway systems from their present vulnerabilities, as they relate to the National Institute of Standards and Technology (NIST) Cybersecurity Framework. The fact that many of them are very basic and obvious to cybersecurity professionals is just an indication of frequently low cybersecurity and cyber-kinetic security maturity of railways around the world.
Detect
Issues to consider:
- Anomalies and Events
- Security Continuous Monitoring
- Detection Processes
Recommended priorities:
- Design security operations for rapid detection and triage.
- Expand detection to network flows from just logs.
- Expand detection to ICS, making sure to consider all security and resilience issues that apply to ICS.
- Utilize threat intelligence (both, strategic and tactical) and industry collaboration to improve detection.
- Assess cybersecurity on a continuous/regular basis, including multiple types across VA, people, process to red teaming.
- Explore mechanisms to detect intentional electromagnetic interference (IEMI) attacks, if justified by the Threat, Vulnerability and Risk Assessment (TVRA).
Respond
Issues to consider:
- Response Planning
- Communications
- Mitigation
- Improvements
Recommended priorities:
- Establish cybersecurity response playbook (operation and IT level).
- Strengthen the linkage between cybersecurity response and emergency, incident and crisis management processes.
- Engage third-party expertise for incident response, digital forensics, crisis communication, etc.
- Conduct regular and comprehensive cyber-crisis exercises, including all relevant railway functions (primarily OT and IT) as well as third-party responders and key suppliers.
Recover
Issues to consider:
- Recovery Planning
- Improvements
- Communications
Recommended priorities:
- Develop Business Impact Assessment (BIA) and Business Continuity Planning (BCP).
- Disaster Recovery Planning.
- Develop comprehensive and regularly tested backup and restore practices.
- Include third-party suppliers in recovery planning and recovery activities.
- Feed recovery lessons learned back into problem management.
Takeaways
Much is being done to reduce the cyber-kinetic vulnerabilities that fully cyber-enabled railway systems potentially offer. But much more needs to be done. Fully cyber-enabled railway systems offer attackers a range of vulnerabilities perhaps unmatched by any other type of industrial control system.
And potential attackers are well aware of their opportunities, as Project HoneyTrain demonstrates. Prevention is the best form of defense. Victims that are most vulnerable will be attacked first. Those systems that do not want to fall victim to disasters that could well dwarf the noncyber tragedies that have been occurring on rail lines need to be vigilant in their efforts to make – and keep – their cyber-systems secure.
For over 30 years, Marin Ivezic has been protecting people, critical infrastructure, enterprises, and the environment against cyber-caused physical damage. He brings together cybersecurity, cyber-physical systems security, operational resilience, and safety approaches to comprehensively address such cyber-kinetic risk.
Marin leads Industrial and IoT Security and 5G Security at PwC. Previously he held multiple interim CISO and technology leadership roles in Global 2000 companies. He advised over a dozen countries on national-level cybersecurity strategies.